TRITON’s Tactics and Techniques in the Enterprise domain + mitigations – Part 3

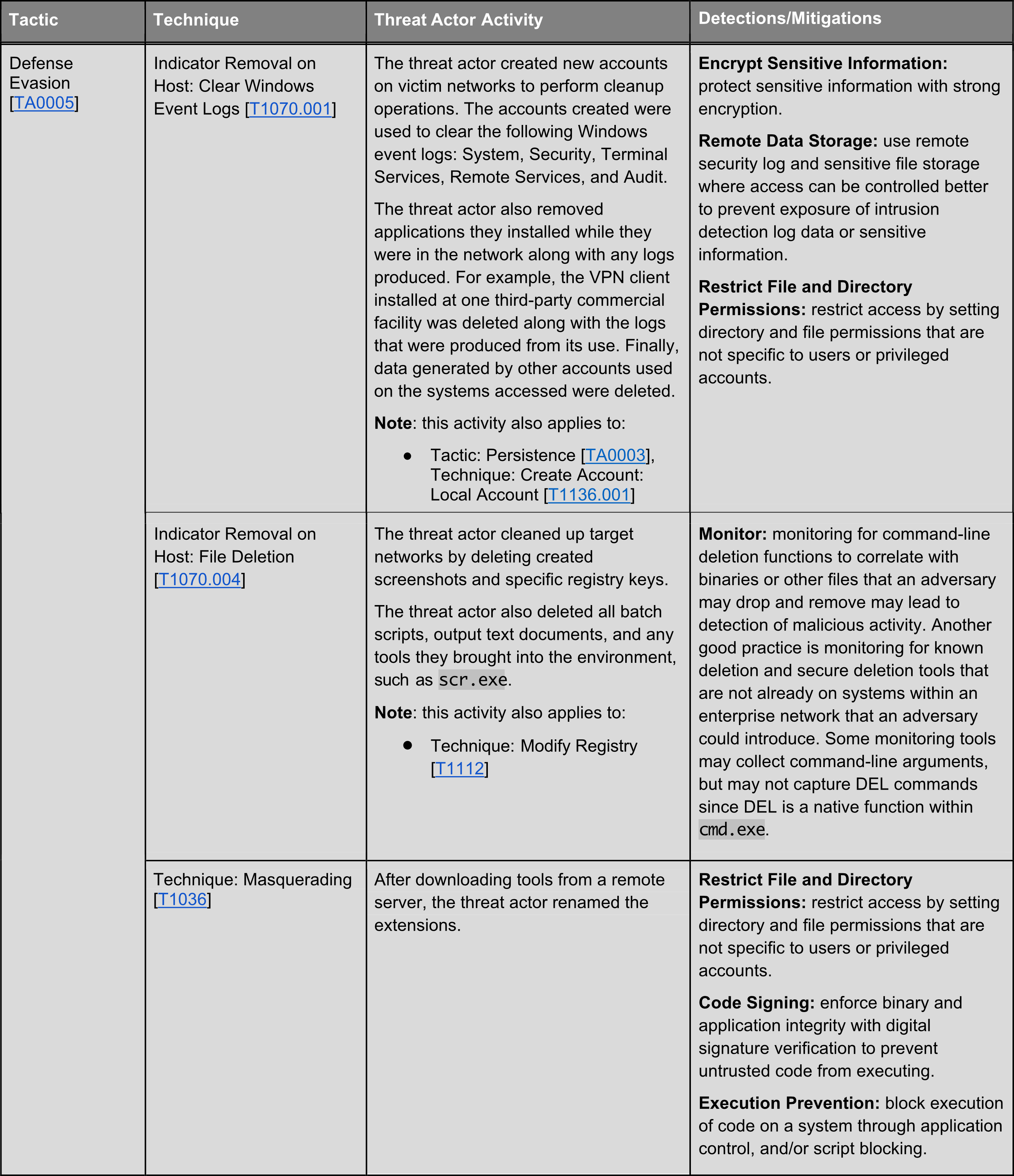
In part 3 of the TRITON tactics and technics series come the Defense Evasion techniques which seek to help the malware bypass defensive tools’ detection. These techniques have been mapped by MITRE ATT&CK in their universally renowned knowledge base of adversary tactics and techniques based on real-world observations.
As a reminder, TRITON malware was first identified during an attack on a Saudi Arabian petrochemical plant facility in the year 2017 and it targets Schneider Electric’s Triconex Tricon controllers. This was the first time in history that safety instrumented systems were targeted with the intention to fail, potentially leading to serious damage to property and humans.
Next week, we will present the Credential Access Techniques of the TRITON malware.
About this article
This article was based on a Cybersecurity Advisory by CISA. You can read the full CSA here.



0 Comments